No products in the cart.
Introduction
MATLAB is a multi-paradigm numerical computing environment and proprietary programming language developed by MathWorks. MATLAB allows matrix manipulations, plotting of functions and data, implementation of algorithms, creation of user interfaces, and interfacing with programs written in other languages.
In our day-to-day life, we are sending and receiving much information from the internet. This information is transmitting through a transmission line, this channel is always insecure, and anything can be seen by anyone, not only just seeing they can actually modify the data.
In this insecure channel, all our information is not actually passed by what we send. Data will be encrypted before sending it into the channel, and the encrypted is transferred through the transmission line. Now even if anyone captures the data, then they will get the encrypted data and not the actual data.
You might get one question of how the actual receiver will get the actual data? Yes, without the key and algorithm used by the sender, it is impossible to retrieve the actual data.
Description

Symmetric encryption was the only type of encryption in the 1970’s. Before beginning, we define some terms. An original message is called Plaintext, while the coded message is called Cipher text. The process of converting from plaintext to cipher text is known as Encryption or Enciphering; restoring the plaintext from the cipher text is Decryption or Deciphering.
During encryption, the sender uses the algorithm and key to encrypt the data,
C=E (K, P)
Where, C is cipher (the encrypted data);
E is encryption algorithm;
K is the secret key
P is plaintext (the actual data).
Now, assume the receiver knows the key and the ciphertext. Decryption is the process of retrieving the actual data from the cipher. It is the exact reverse process of encryption,
P=D (K, C)
Where, P is plaintext (the actual data);
D is the decryption algorithm;
K is the secret key;
C is cipher (the encrypted data).
Points to be remembered:
- The same algorithm with the same key is used for encryption and decryption.
- The sender and receiver must share the algorithm and the key.
- The key must be kept secret.
- It must be impossible or at least impractical to decipher a message if no other information is available.
- Knowledge of the algorithm plus samples of ciphertext must be insufficient to determine the key.
Code
Get Access to
Code & Report!
Implement a real-time Symmetric Key Cryptography system where we send and receive data securely using MATLAB; Developed with MATLAB R2019b
Here, we considered an encryption process where we use the Fibonacci series. The encryption algorithm process is as follows:
Fibonacci Function
Step1: Creating a function that generates a Fibonacci series with same length of plaintext
Here, l=length of plaintext
f=array of Fibonacci series
Sender
Step2: Creating cipher, an array of elements by adding the given key, the generated Fibonacci series, and the plain text
Here, k=Key(an alphabet)
ptext=plain text
Step3: Creating a text file containing the generated cipher text which will be shared to the receiver via transmission line.
Receiver
Step4: Copying the content of text file that is shared into the cipher array
Step5: Decrypting the cipher by subtracting the key, the Fibonacci series of same length as cipher text from the cipher. The resultant array containing integer numbers(ASCII values) should be converted to characters
Result
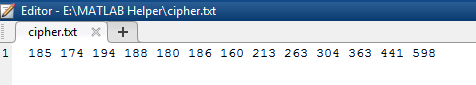
The sender wants to send the plaintext as MATLAB Helper, and the key is k.

After running the sender side code, a confirmation message was printed on the screen
Now, the text file will contain the cipher text
The receiver should enter the correct key k

Now receiver retrieved the plaintext back
If the receiver enters a wrong key, say x

Now, the receiver got a wrong plaintext.
So, the key should be kept secret. We can interpret this key with our house key, whoever has the access of key can enter into the house likewise here also without knowing the key we cannot know the plaintext
Conclusion
In Cryptography all encryption algorithms are based on two general principles: substitution, in which element in the plaintext is mapped into another element, and transposition, in which elements in the plaintext are rearranged. The fundamental principle is that no information be lost
An encryption algorithm can strive for is an algorithm that meets one or both of the following criteria:
- The cost of breaking the cipher exceeds the value of the encrypted information.
- The time required to break the cipher exceeds the useful lifetime of the information.
An encryption scheme is said to be computationally secure if either of the foregoing two criteria are met.
Thus, we successfully transmitted the data securely in an insecure channel using symmetric-key cryptography in MATLAB.
Get instant access to the code, model, or application of the video or article you found helpful! Simply purchase the specific title, if available, and receive the download link right away! #MATLABHelper #CodeMadeEasy
Ready to take your MATLAB skills to the next level? Look no further! At MATLAB Helper, we've got you covered. From free community support to expert help and training, we've got all the resources you need to become a pro in no time. If you have any questions or queries, don't hesitate to reach out to us. Simply post a comment below or send us an email at [email protected].
And don't forget to connect with us on LinkedIn, Facebook, and Subscribe to our YouTube Channel! We're always sharing helpful tips and updates, so you can stay up-to-date on everything related to MATLAB. Plus, if you spot any bugs or errors on our website, just let us know and we'll make sure to fix it ASAP.
Ready to get started? Book your expert help with Research Assistance plan today and get personalized assistance tailored to your needs. Or, if you're looking for more comprehensive training, join one of our training modules and get hands-on experience with the latest techniques and technologies. The choice is yours – start learning and growing with MATLAB Helper today!
Education is our future. MATLAB is our feature. Happy MATLABing!
The implementation of the Fibonacci series for encryption process was a great idea and overall a well structured algorithm for symmetric key cryptography.